Learn about fingerprint authentication!
Click on the buttons below to learn more about each topic of fingerprint authentication :)
Origins of Fingerprint Authentication
The origins of fingerprint authentication can be traced back to ancient civilizations. Around 2000 BC, in ancient Babylon, fingerprint impressions were used as signatures on clay tablets for business transactions. However, it was in the late 19th century that the systematic study of fingerprints gained momentum. Sir Francis Galton, a British scientist, conducted extensive research on fingerprints, emphasizing their uniqueness and permanence. His work laid the foundation for modern fingerprint identification.Sir Edward Henry, a British police official, is credited with the development of a classification system based on fingerprint ridge patterns. However, recent studies show this may be false, as two Indian police officers, Azizul Haque and Hem Chandra, developed a similar system 5 years before Henry (1916). This system, introduced in the early 20th century, became a standard for fingerprint identification, and it remains in use today.One of the earliest classifications of fingerprints comes from the Samudrika Shastra, an Indian astrological text depicting the relationship between physical characteristics and life experiences. Below is an early fingerprint categorization table from this text.

In the United States, the use of fingerprints for criminal identification began in the early 20th century, with New York's Civil Service Commission establishing the first systematic fingerprint file in 1901. By 1904, fingerprints were widely adopted by law enforcement agencies across the country. The digital age brought significant advancements with the development of automated fingerprint identification systems (AFIS) in the late 20th century, replacing manual classification and matching with computer-based methods for enhanced accuracy and efficiency.Fingerprint recognition's journey continued as it transitioned from criminal identification to consumer devices. Apple's introduction of Touch ID in 2013 with the iPhone 5s marked a pivotal moment, making fingerprint authentication a mainstream and accessible technology. Today, many countries worldwide have integrated fingerprint authentication into national identity systems, passports, and border controls, strengthening security and reducing identity fraud. The evolution of fingerprint authentication reflects its enduring importance in modern technology and security, with ongoing advancements in accuracy and additional features.
Types of Fingerprints
There are three main categories of fingerprints: arches, loops, and whorls. Loops are the most common types of fingerprints, they are found in about 60-70% of the population. Whorls are found in about 30% of the population, and arches are found in 5-10%.Arches:
Plain Arch: This is the simplest fingerprint pattern. It consists of ridges that flow from one side to the other with no defined core or delta (triangular ridge pattern).
Tented Arch: The tented arch has a more prominent and sharper peak or tented appearance in the center. It lacks a defined core or deltaLoops:
Radial Loop: In a radial loop, the ridges flow in the direction of the thumb. The core is located near the thumb, and the delta is towards the little finger.
Ulnar Loop: Ulnar loops have ridges that flow in the direction of the little finger . The core is near the little finger, and the delta is located near the thumb.Whorls:
Plain Whorl: This pattern consists of ridges that encircle a central core or delta. Plain whorls can be classified further into central pocket loop whorls or central plain whorls, depending on the exact location of the core.
Double Loop: Double loops consist of two separate loop patterns with two separate and distinct cores and deltas. They are often interconnected.
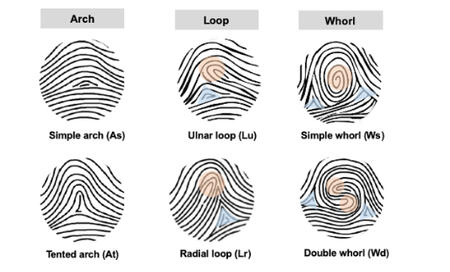
Considering the image above, take a look at your own fingerprint. Which one does your fingerprint fall under? Once you have decided, fill out the poll below to see the percentage of people in this class with different fingerprint types.
Biometric Authentication Systems Following the Fingerprint
Facial Recognition: Facial recognition technology has become more prevalent, especially in security and mobile device authentication. It analyzes unique facial features, such as the distance between the eyes and the shape of the face to authenticate a user.Iris Recognition: Iris recognition systems scan the unique patterns in a person's iris. Iris recognition is known for its accuracy and is used in secure access control systems and border security.Voice Recognition: Voice recognition technology analyzes the unique characteristics of an individual's voice, such as pitch and tone. It is used in applications like phone-based authentication and voice-controlled devices.Palmprint Recognition: Palmprint recognition analyzes the unique patterns in the palm of a person's hand. It is used in applications like access control and forensic investigations.Retina Scans: Retina scans examine the patterns of blood vessels in the thin layer of tissue at the back of the eye. This technology is used in high-security applications, such as access to classified facilities.Vein Recognition: Vein recognition systems use the unique patterns of veins in the palm or back of the hand for authentication. It is employed in secure access control and financial transactions.Ear Recognition: Ear recognition technology analyzes the unique shape and features of the ear. It is used in forensic science and law enforcement.